
Precision has carefully invested into and nurtured the capabilities and resources required, such as its PIVOT IoT Framework, embedded engineering, software engineering, implementation and support infrastructure, to provide end to end solution IoT solutions
The Internet of Things (IoT) is a network of devices which have embedded electronics, sensors, actuators & software and network connectivity, enabling exchange and collection of data. These devices can therefore be monitored and controlled remotely. Implementation of IoT technologies is expected to help create solutions delivering higher efficiencies, higher accuracy of data and economic benefits through cost savings while reducing the need for human intervention.
IoT solutions range across consumer IoT, industrial IoT, healthcare IoT, Smart Cities and several other areas.
Precision brings its more than two & a half decades of experience in the IT industry to assist in your IoT journey. Precision has carefully brought together, invested into and nurtured the capabilities and resources required, such as its PIVOT IoT Framework, embedded engineering, software engineering, implementation and support infrastructure, to be able to provide an end to end IoT solution.
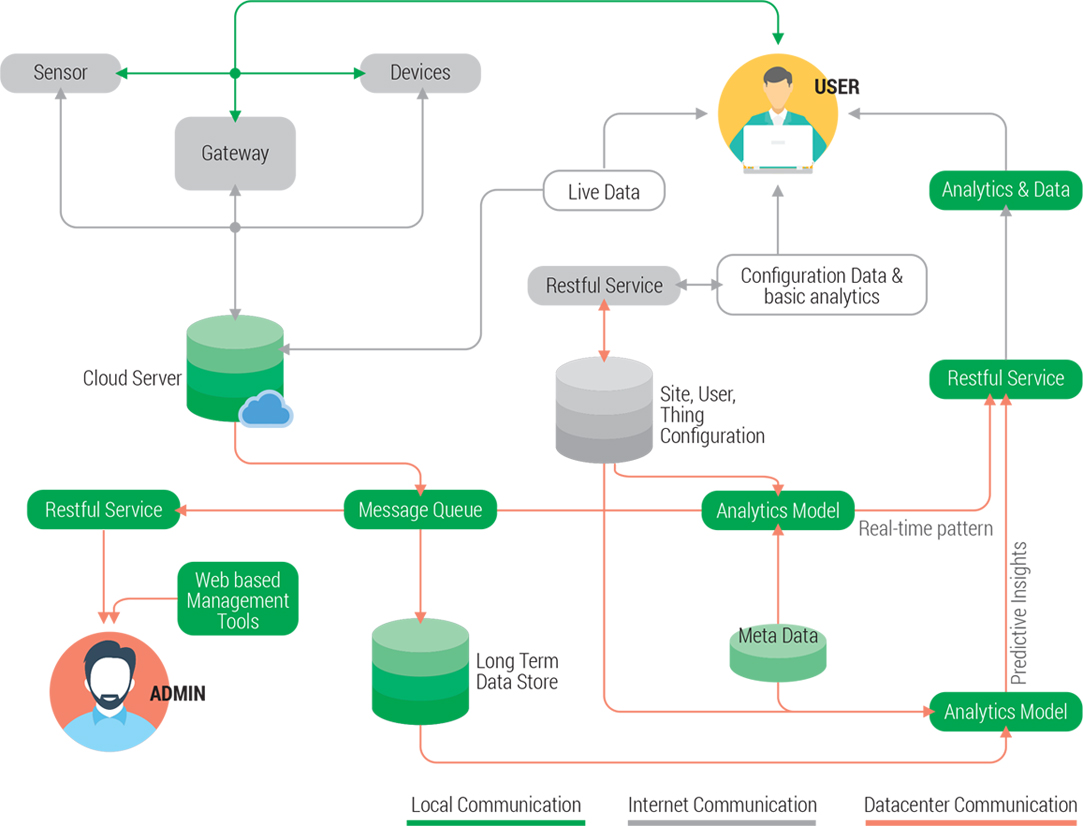
PIVOT is Precision’s end-to-end, modular, value added IoT framework, which has been designed to adapt rapidly and easily to IoT solution needs, be it Industrial IoT, Enterprise IoT, Consumer IoT or Smart City solution.
PIVOT employs best-in-class tools and techniques to deploy & connect to ‘things’, monitor and manage them, to develop & deploy applications supporting operations, to ingest large amounts of data and to provide rich analytics.
Precision employs widely used protocols in PIVOT and shall keep enhancing the protocol stack in line with the industry trends and optimized applicability. PIVOT implements Web sockets and supports MQTT, CoAP & Modbus. In terms of Security, PIVOT secures different layers of its architecture through appropriate standards such as role based user authentication, Site IDs, Site Authentication Codes, SSL, WPA2 and so forth.
Precision can address the end-to-end requirements of your IoT innovation, across all layers of the solution stack:
Precision can not only help you design, architect, prototype and refine your IoT solution; we can actually help you deploy the solution and help support it through our pan-India support network. We’ve got you truly covered!
Precision employs PIVOT – Precision’s Value Added Internet of Things Framework to develop Smart Home solutions.
Precision can help you all along your journey of envisioning, preparing, prototyping, architecting and implementing your IoT solutions. Be it a solution being implemented as a project or making your products ‘smart’, Precision would be keen to partner with you.
A sample of our PIVOT based solutions for Smart Home:

These switches replace conventional electrical switches and offer benefits such as local & ‘remote’ control, scheduled operations, improved energy efficiency, convenience, safety and security

Enabling IoT in conventional luminaires, to deliver the benefits of energy efficiency, safety, control & convenience, cost optimization & actuation based on sensor inputs and analytics. Precision has also developed a Power over Ethernet (PoE) based solution to drive power to LED luminaires through Ethernet cables as opposed to the standard AC supply, thereby taking the concepts of safety & energy efficiency to higher levels

Transitioning consumer durables to ‘smart products’. Features include sensor integration, state monitoring and control of the device, energy monitoring and usage analysis, direct, gateway and cloud based operations, degradation and failure event monitoring and preemptive alerts and more

Real time energy usage monitoring (for specific equipment or overall). Real time load monitoring, threshold configurations and breach alerts. Event detection & reporting
The segments that we address are:
Precision employs PIVOT – Precision’s Value Added Internet of Things Framework to develop Smart Building solutions.
Precision can help you all along your journey of envisioning, preparing, prototyping, architecting and implementing your IoT solutions. Be it a solution being implemented as a project or making your products ‘smart’, Precision would be keen to partner with you.
A sample of our PIVOT based solutions for Smart Building:

These switches replace conventional electrical switches and offer benefits such as local & ‘remote’ control, scheduled operations, improved energy efficiency, convenience, safety and security

Enabling IoT in conventional luminaires, to deliver the benefits of energy efficiency, safety, control & convenience, cost optimization & actuation based on sensor inputs and analytics. Precision has also developed a Power over Ethernet (PoE) based solution to drive power to LED luminaires through Ethernet cables as opposed to the standard AC supply, thereby taking the concepts of safety & energy efficiency to higher levels
Solutions include Smart Car Parking, Air Conditioning System, Medical Equipment Management (Healthcare), Smart Rooms (Hospitality) and others

Real time energy meter data transmission (push/pull), Power consumption analysis & alerts (to enable preventive maintenance), Real time load monitoring, threshold configurations and breach alerts. Event detection & reporting
The segments that we address are:
Precision employs PIVOT – Precision’s Value Added Internet of Things Framework to develop Smart Industry solutions.
Precision can help you all along your journey of envisioning, preparing, prototyping, architecting and implementing your IoT solutions. Be it a solution being implemented as a project or making your products ‘smart’, Precision would be keen to partner with you.
A sample of our PIVOT based solutions for Smart Industry:

Replace conventional electrical switches with smart switches. Centralized monitoring (of present state) and control. Can be combined with energy monitoring module for added benefits

Real time energy usage monitoring for plant equipment, Real time equipment usage information, power consumption analysis & alerts (to enable preventive maintenance) sensor integration, threshold configurations and breach alerts. Event detection & reporting
Measurement of parameters such as temperature, relative humidity, light levels. Threshold configurations and breach alerts

Integration of IoT solution with plant equipment and machinery through existing sensors and management ports. Centralized dashboard for monitoring state of machinery and control (where feasible)
The segments that we address are:
Precision employs PIVOT – Precision’s Value Added Internet of Things Framework to develop Smart City solutions.
Precision can help you all along your journey of envisioning, preparing, prototyping, architecting and implementing your IoT solutions. Be it a solution being implemented as a project or making your products ‘smart’, Precision would be keen to partner with you.
A sample of our PIVOT based solutions for Smart City:

Particulate Matter, CO2, CO, O2, Temperature, Humidity, Atmospheric Pressure, other sensors as needed (O3, SO2, CH4, NO2). Interval based or real-time streaming of data, threshold configurations and breach alerts and more

Measurement of parameters such as pH, DO, ORP, Turbidity, Ions (ex: Ca, Fl, Cl), optional sensors for NH4, Bromide, Iodide, Cupric, Fluoroborate and others. Threshold configuration based on WHO recommendations and breach alerts

Continuous measurement of precipitation using a weighing system. Threshold settings and intensity alarms
Measurement of moisture levels, pH and light levels. Base data analysis to determine whether the soil is arable

Real time energy meter data transmission (push/pull). Real time load monitoring, threshold configurations and breach alerts. Event detection & reporting
The segments that we address are:
Do contact us to start a conversation about your IoT initiative and we would be happy to understand the use case and design a solution for your specific needs.